According to blackkite.com, every single supplier breach now claims an average of 5.28 downstream victim organizations, the highest multiplier ever recorded by Black Kite’s research — underscoring the accelerating scale of cascading cyber risk across global supply chains.
The Limits of Compliance-First Supply Chain Risk Management
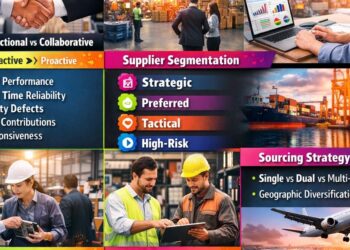
Black Kite identifies a critical gap in conventional third-party cyber risk management (C-SCRM): reliance on static frameworks and periodic assessments fails to capture real-time exposure. While standards like NIST SP 800-161 define rigorous processes, the source states they “tell you what controls should be in place, not what’s actually happening inside your supplier ecosystem right now.” Documented compliance and real cyber visibility are not the same thing.
Two Overlooked Threats: Cascading and Concentration Risk
- Cascading risk: A cyber event at one supplier ripples outward — into your systems, your customers’ systems, and those of every other organization depending on the same underlying provider. As Black Kite’s research shows, this ripple effect now impacts 5.28 downstream victims per breach.
- Concentration risk: Occurs when too many suppliers depend on shared technology, infrastructure, or Nth-party providers. Black Kite’s 2026 research found that 70% of top 50 vendors shared by the Global 2000 carry at least one unpatched vulnerability from the CISA KEV catalog, and 62% have leaked credentials on the dark web.
Going Beyond Direct Suppliers: Nth-Party Visibility
Most supply chain risk programs stop at tier-1 suppliers — but risk extends further. Black Kite’s Supply Chain module automatically maps fourth-, fifth-, and Nth-party relationships, surfacing hidden dependencies and concentration points. This capability enables teams to move beyond framework compliance toward continuous, intelligence-driven risk management.
Real-Time Intelligence for Proactive Response
Black Kite’s Ransomware Susceptibility Index® (RSI™) analyzes technical and behavioral indicators to assess a supplier’s susceptibility to ransomware. Its FocusTags® flag supply chain events the moment they emerge — such as during the MOVEit exploitation or CrowdStrike outage — enabling customers to identify exposed suppliers in real time and act immediately.
Source: blackkite.com
Compiled from international media by the SCI.AI editorial team.